Initial Configuration of CubeBackup for Microsoft 365 on Windows
This article will guide you through the initial configuration of CubeBackup for Microsoft 365 on Windows. If you are using CubeBackup on Linux or in a Docker container, please refer to Initial configuration CubeBackup for Microsoft 365 on Linux or Initial Configuration of CubeBackup for Microsoft 365 using Docker.
Step 1. Open the CubeBackup web console
After CubeBackup has been installed, the web console will automatically pop up in your default web browser. You can also open the web console by either clicking the CubeBackup icon on the desktop, or by visiting http://<server-ip>:<port> on any web browser within your network.
If permitted by your company's firewall policy, it can also be accessed from outside your network at http://<server_external_ip>:<port> or an assigned domain name.
The default web console address is http://<server_ip>. If port 80 is already in use, the installation wizard will ask you to assign a different port.
Step 2. Set backup location
CubeBackup allows you to back up Microsoft 365 data to either on-premises storage or your private cloud storage.
Currently, CubeBackup supports backing up to a local disk, NAS/SAN, Amazon S3 storage, Microsoft Azure Blob storage, Google Cloud Storage and Amazon S3-compatible storage. Please click the corresponding tab for detailed instructions.
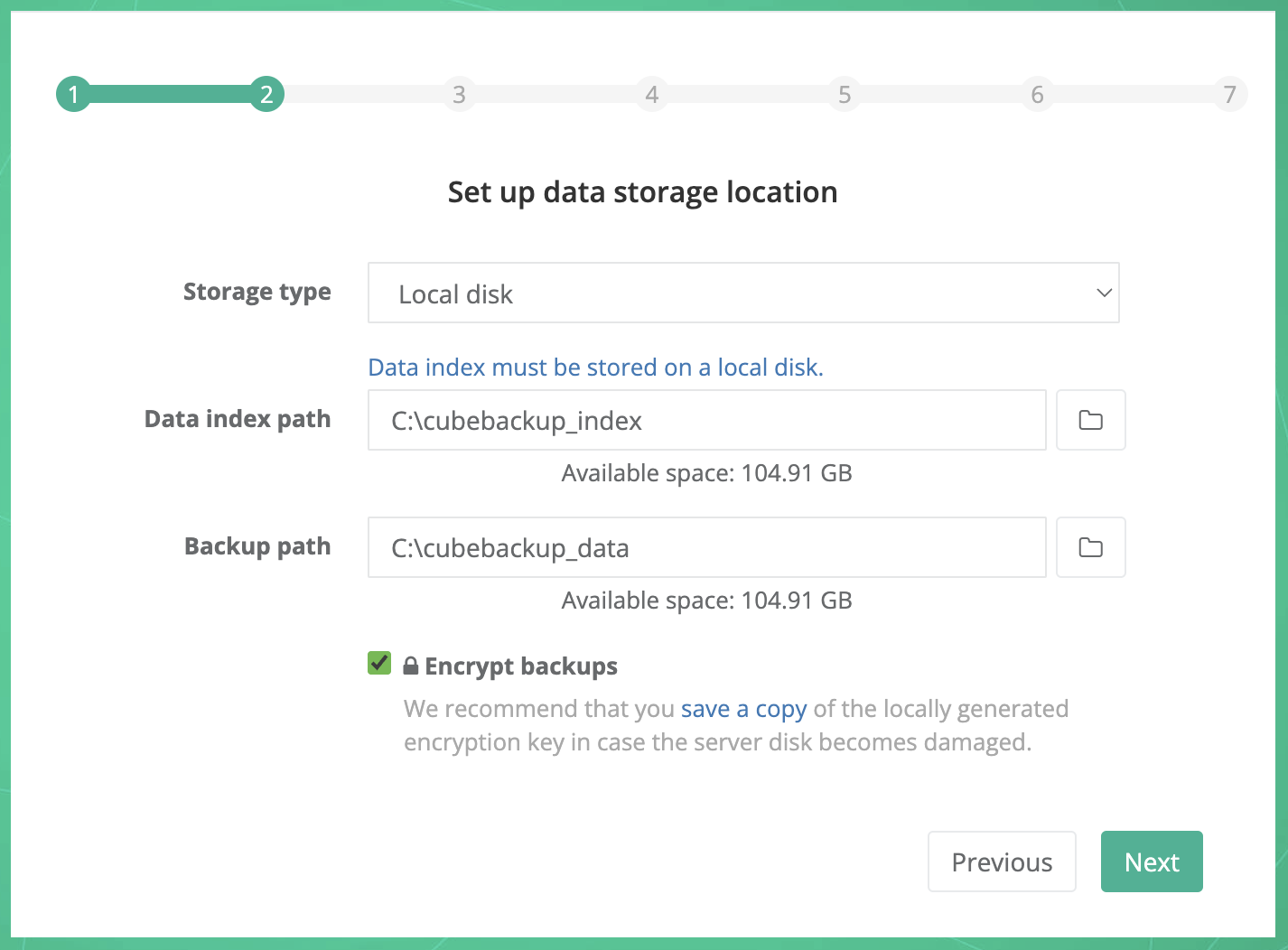
Storage type: Select Local disk from the dropdown list.
Data index path: Select a local directory to store metadata for your backup.
Note: Since the data index contains the metadata for the backups, access speed is crucially important for the performance of CubeBackup. We strongly recommend that you store the data index on a local SSD. See What is the data index for more information.
Backup path: Select the local storage destination for your Microsoft 365 backup data.
Note: Please ensure the backup location has sufficient space to store the data for all users and groups in your Microsoft 365 organization, including any future backups. Since CubeBackup itself keeps a revision history of files, a good rule of thumb is to reserve 2x the estimated data size for your organization. For example, if there are 100 users in your organization and each user has 10Gb of data on average, there should be at least 100 * 10GB * 2 = 2TB of space available for the backup. To estimate the total data size of your Microsoft 365 organization, please see how to check your Microsoft 365 storage usage .
Encrypt backups: If you want your backups to be stored encrypted, make sure the "Encrypt backups" option is checked.
Tips:
1. Before clicking Next in the CubeBackup setup wizard, we recommend that you download a copy of the encryption key file using the link provided and store it in a separate, safe location. The key is generated locally and is not stored anywhere except on your servers, which means that we at CubeBackup cannot help you if your key file is lost or damaged through server corruption or natural disaster. For more information about rebuilding your CubeBackup instance in the event of a disaster, see: Disaster recovery of a CubeBackup instance .
2. This option cannot be changed after the initial configuration.
3. Data transfer between Microsoft Azure and your storage is always HTTPS/SSL encrypted, whether or not this option is selected.
4. Encryption may slow down the backup process by around 10%, and cost more CPU cycles.
When all information has been entered, click the Next button.
Note: If you plan to back up your Microsoft 365 data to Windows network storage, we strongly recommend storing the data index on an SSD on your local server, and be sure to keep a stable network connection with the NAS to avoid interrupting the backup process, which might result in corrupted files in your backup repository. This storage type is not as stable as cloud storage, please use at your own risk.
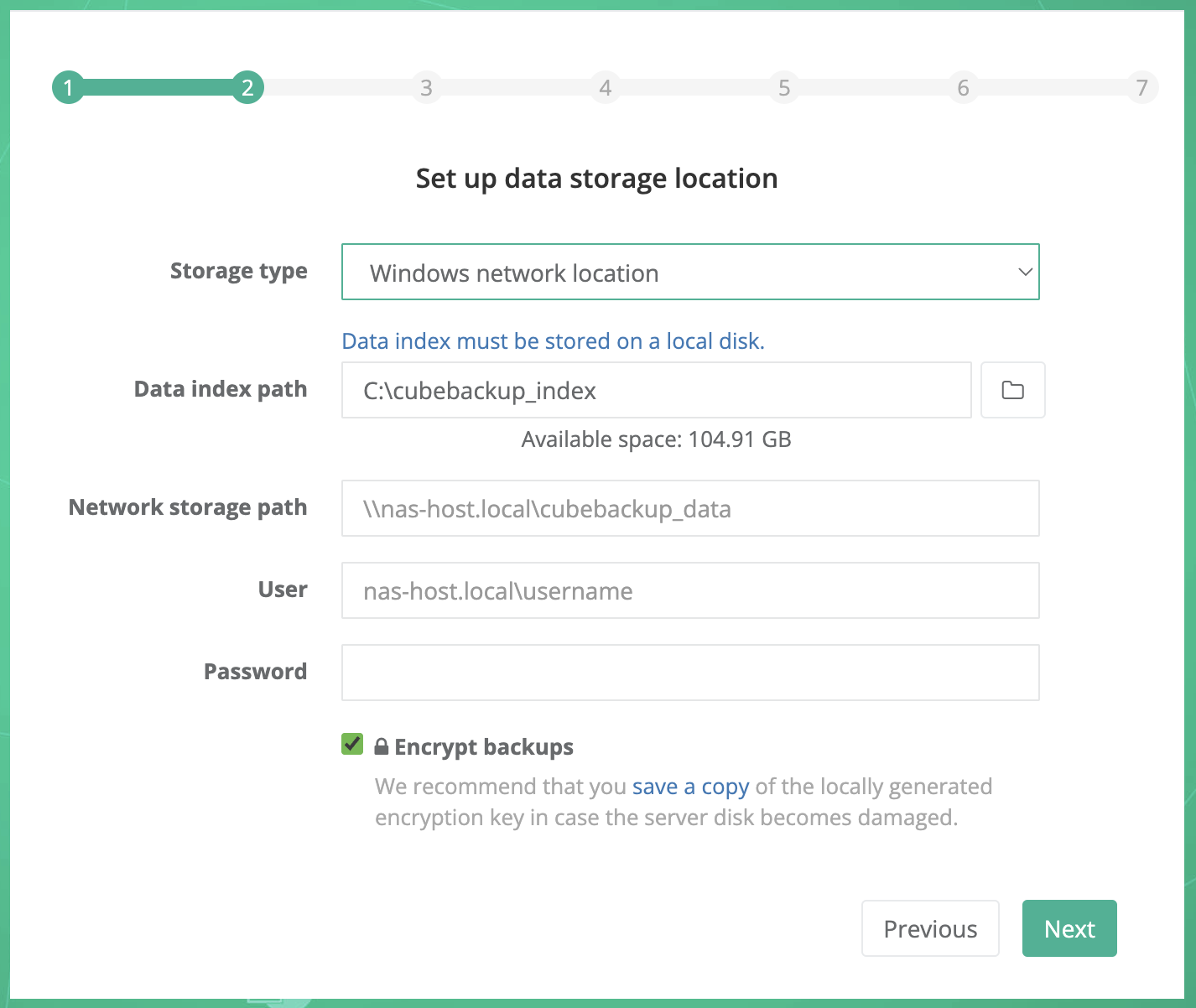
Storage type: Select Windows network location from the dropdown list.
Data index path: Select a local directory to store metadata for your backup.
Note: Since the data index contains the metadata for the backups, access speed is crucially important for the performance of CubeBackup. We strongly recommend that you store the data index on a local SSD. See What is the data index for more information.
Network storage path: Manually enter the UNC path for the remote storage, (e.g. \\NAS-HOSTNAME\microsoft365_backup or \\192.168.1.123\microsoft365_backup). Generally, a hostname is preferred over a numeric IP address, especially in an Active Directory domain environment.
Notes:
1. Currently, a mapped drive letter for the network resource is not supported. Please be sure to use the UNC path (e.g. \\NAS-HOSTNAME\microsoft365_backup) instead of a mapped drive (e.g. Z:\microsoft365_backup).
2. Please ensure the backup location has sufficient space to store the data for all users and groups in your Microsoft 365 organization, including any future backups. Since CubeBackup itself keeps a revision history of files, a good rule of thumb is to reserve 2x the estimated data size for your organization. For example, if there are 100 users in your organization and each user has 10Gb of data on average, there should be at least 100 * 10GB * 2 = 2TB of space available for the backup. To estimate the total data size of your Microsoft 365 organization, please see how to check your Microsoft 365 storage usage .
User and password: The username and password to access the network storage.
- For Windows networks using Active Directory, the format of username should <Domain_name>\<User_name>. For example, cubebackup\user is preferred while [email protected] is not supported.
- For Windows networks organized by workgroup, or if the network storage is located outside of your active directory, the format of username should be <NAS_Hostname>\<User_name>. For example, backup_nas\user.
Why are a username and password required?
CubeBackup runs as a service using the system default local service account, which, by design, has not been granted access rights to network resources in Windows. In order for CubeBackup to backup and restore data in your network storage, a username and password must be supplied.
Encrypt backups: If you want your backups to be stored encrypted, make sure the "Encrypt backups" option is checked.
Tips:
1. Before clicking Next in the CubeBackup setup wizard, we recommend that you download a copy of the encryption key file using the link provided and store it in a separate, safe location. The key is generated locally and is not stored anywhere except on your servers, which means that we at CubeBackup cannot help you if your key file is lost or damaged through server corruption or natural disaster. For more information about rebuilding your CubeBackup instance in the event of a disaster, see: Disaster recovery of a CubeBackup instance .
2. This option cannot be changed after the initial configuration.
3. Data transfer between Microsoft Azure and your storage is always HTTPS/SSL encrypted, whether or not this option is selected.
4. Encryption may slow down the backup process by around 10%, and cost more CPU cycles.
When all information has been entered, click the Next button.
Note: If you plan to back up your Microsoft 365 data to Amazon S3 storage, we strongly recommend running CubeBackup on an AWS EC2 instance (e.g. t3.large instance) instead of a local server. Hosting both the backup server and storage on AWS will avoid the bottleneck of all data moving through your local server and greatly improve backup speeds.
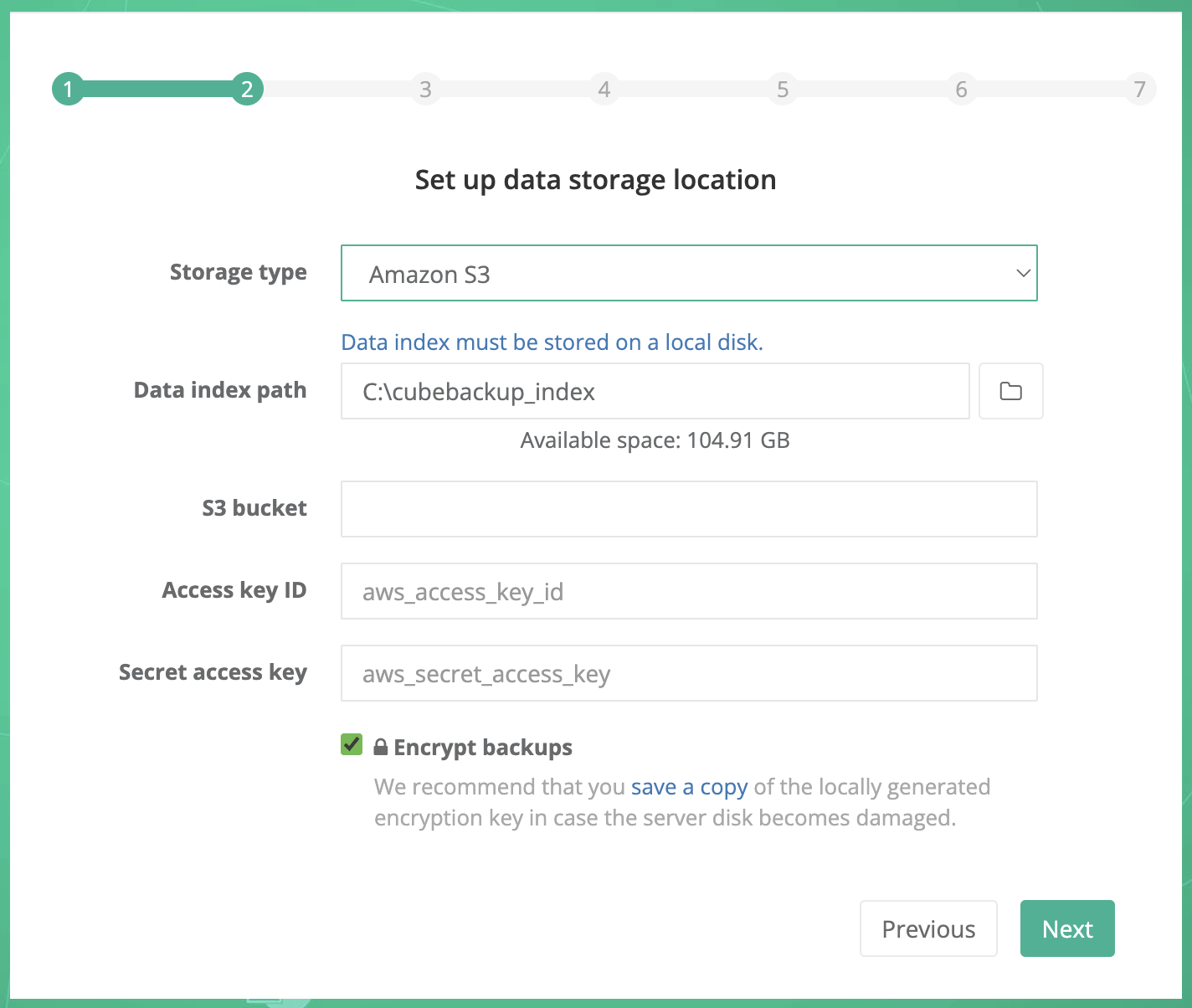
Storage type: Select Amazon S3 from the dropdown list.
Data index path: Select a local directory to store metadata for your backup.
Note: Data index is the metadata for the backups, and its accessing speed is crucially important for the performance of the backups. We strongly recommend that you store the data index on a local SSD. See What is the data index for more information.
S3 bucket: The unique name of your S3 storage bucket.
Access key ID: The AWS IAM access key ID to authorize access to data in your S3 bucket.
Secret access key: The secret of your AWS IAM access key.
Please follow the instructions below to create and configure a private Amazon S3 bucket for your backup data.
- Create an AWS account
If your company has never used Amazon Web Services (AWS) before, you will need to create an AWS account. Please visit Amazon Web Services (AWS) , click the Create an AWS Account button, and follow the instructions.
If you already have an AWS account, you can sign in directly using your account.
- Create an Amazon S3 bucket
Amazon S3 (Amazon Simple Storage Service) is one of the most-widely used cloud storage services in the world. It has been proven to be secure, cost-effective, and reliable.
To create your S3 bucket for Microsoft 365 backup data, please follow the brief instructions below.
- Open the Amazon S3 console using an AWS account.
- Click Create bucket.
- On the Create bucket page, enter a valid and unique Bucket Name.
- Leave the other available options as they are.
Note:
1. Since CubeBackup already has a version control and will overwrite index files frequently, enabling Bucket Versioning or Advanced settings > Object Lock in the S3 bucket will result in unnecessary file duplication and cost. We recommend leaving these two features disabled.
2. Depending on your company policies, you can change the other default configurations (Block Public Access, Default encryption, etc.). These options will not affect the functioning of CubeBackup. - Ensure that your S3 settings are correct, then click Create bucket.
- Go back to the CubeBackup setup wizard and enter the name of this newly-created bucket.
- Open the Amazon S3 console using an AWS account.
- Create an IAM account
AWS IAM (Identity and Access Management) is a web service that helps you securely control access to AWS resources. Follow the brief instructions below to create an IAM account for CubeBackup and grant access to your S3 bucket.
- Open the AWS IAM console .
- Select Users from the left panel and click Create user.
- Enter a valid User name (e.g. CubeBackup-S3), leave the option "Provide user access to the AWS Management Console" unchecked, and click Next.
- In the Set permissions page, Select Attach policies directly under Permissions options.
- Search for the AmazonS3FullAccess policy and check the box in front of it. You can leave the Set permissions boundary option as default.
Tip: Instead of using the "AmazonS3FullAccess" policy, you can also create an IAM account with permissions to the specific S3 bucket for CubeBackup only .
- Click Next, review your IAM user settings, then click Create user.
- Click the name of the newly-created user in the list.
- Choose the Security credentials tab on the user detail page. In the Access keys section, click Create access key.
- On the Access key best practices & alternatives page, choose Application running outside AWS, then click Next.
- Set a description tag value for the access key if you wish. Then click Create access key.
- On the Retrieve access keys page, click Show to reveal the value of your secret access key. Copy the Access key and Secret access key values to the corresponding textboxes in the CubeBackup setup wizard.
Encrypt backups: If you want your backups to be stored encrypted, make sure the "Encrypt backups" option is checked.
Tips:
1. Before clicking Next in the CubeBackup setup wizard, we recommend that you download a copy of the encryption key file using the link provided and store it in a separate, safe location. The key is generated locally and is not stored anywhere except on your servers, which means that we at CubeBackup cannot help you if your key file is lost or damaged through server corruption or natural disaster. For more information about rebuilding your CubeBackup instance in the event of a disaster, see: Disaster recovery of a CubeBackup instance .
2. This option cannot be changed after the initial configuration.
3. Data transfer between Microsoft Azure and your storage is always HTTPS/SSL encrypted, whether or not this option is selected.
4. Encryption may slow down the backup process by around 10%, and cost more CPU cycles.
When all information has been entered, click the Next button.
Note: If you plan to back up your Microsoft 365 data to Google Cloud storage, we strongly recommend running CubeBackup on a Google Compute Engine VM (e.g. e2-standard-2 VM) instead of a local server. Hosting both the backup server and storage on Google Cloud will avoid the bottleneck of all data moving through your local server and greatly improve backup speeds.
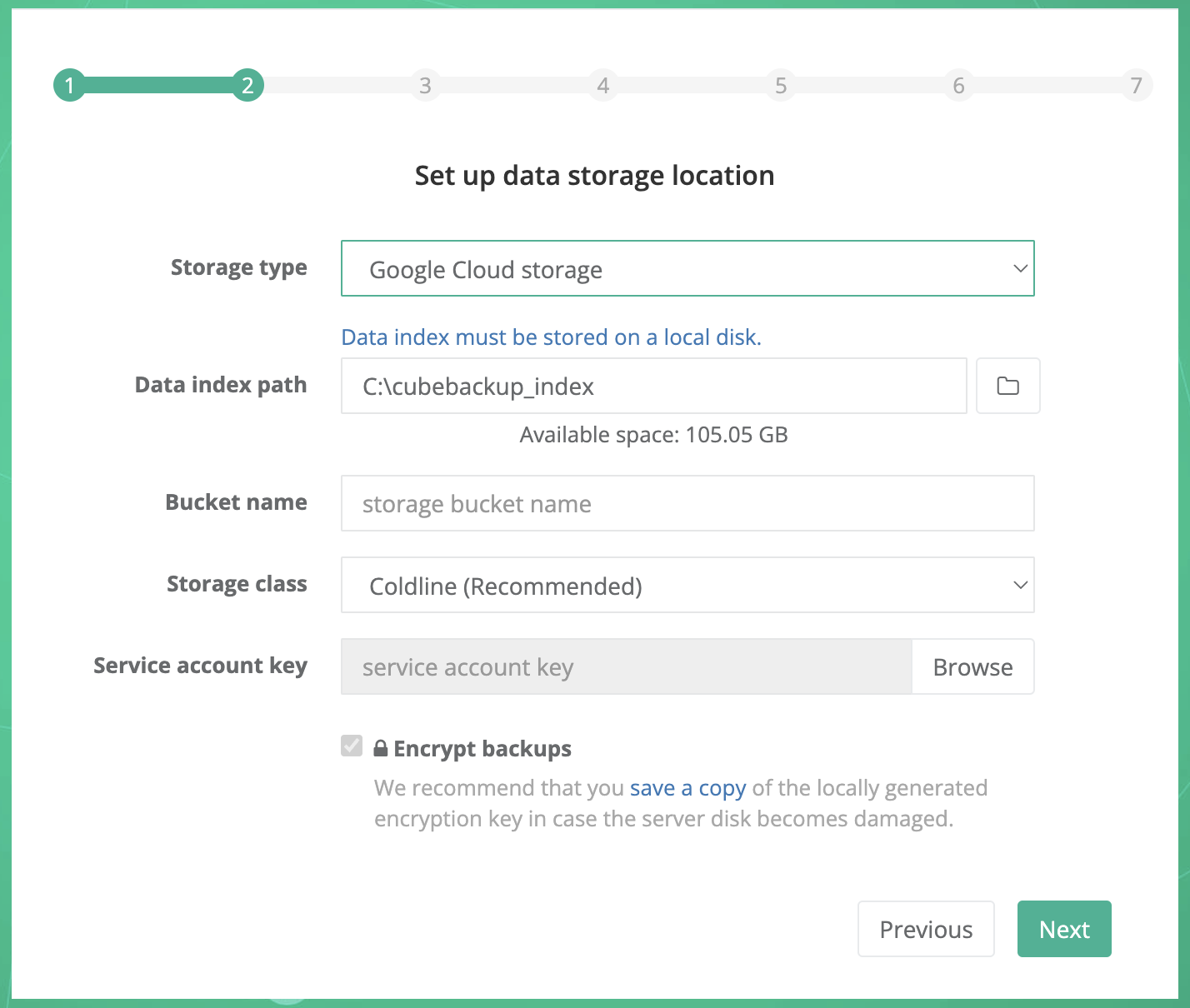
Storage type: Select Google Cloud storage from the dropdown list.
Data index path: Select a local directory to store metadata for your backup.
Note: Since the data index contains the metadata for the backups, access speed is crucially important for the performance of CubeBackup. We strongly recommend that you store the data index on a local SSD. See What is the data index for more information.
Bucket name: Before you can backup data to Google Cloud storage, you will first need to create and configure a private Google Cloud Storage bucket.
Storage class: The storage class for the backup data. Coldline is recommended. For more information about Google Cloud storage classes, please visit Storage classes . You can find the pricing details for the different Google Cloud storage classes at Cloud Storage Pricing .
Service account key: The service account key file to authorize access to data in your Google Cloud storage bucket.
Please follow the instructions or watch the demo below to create a private Google Cloud Storage bucket and the associated service account for CubeBackup.
Google Cloud Platform (GCP) uses projects to organize a group of Google Cloud resources. In this new project, you will create a private storage bucket, and manage permissions for it.
Log in to Google Cloud Platform (GCP) .
Tip: If this is the first time you have used this account, you may need to follow Google's instructions and provide a few additional account details before you can continue.
Go to the Projects page in the Google Cloud Console.
Tip: This page can be opened by either clicking the above link or selecting IAM & admin > Manage resources in the navigation menu. The navigation menu slides out from the left of the screen when you click the
 icon in the upper left corner of the page.
icon in the upper left corner of the page. Click + Create Project, enter a valid Project name, confirm the Organization and Location, then click Create.
The creation of the project may take one or two minutes. After the project has been created, click the newly created project in the Notifications dialog to make it the active project in your dashboard (you can also select your newly created project in the project drop-down list at the top of the page to make it the active project).

For a newly-created project, you will need to enable billing before using Google Cloud Storage. Select the Billing in the navigation menu and follow the prompts to LINK a BILLING ACCOUNT or MANAGE BILLING ACCOUNTS.
- Select Cloud Storage > Buckets from the navigation menu.
- In the Buckets page, click + Create.
- In the Create a bucket page, input a valid name for your bucket, and click Continue.
- Choose where to store your data. Choose a Location type for the bucket, then select a location for the bucket and click Continue.
Tips:
1. CubeBackup is fully compatible with all location types. Depending on the requirements of your organization, you may choose to store backups in single, dual or multi-regions. Details about region plans may be found here
2. Please select the location based on the security & privacy policy of your organization. For example, EU organizations may need to select regions located in Europe to be in accordance with GDPR.
3. If CubeBackup is running on a Google Compute Engine VM, we recommend selecting a bucket location in the same region as your Google Compute Engine VM. - Choose a storage class for your data. We recommend selecting Set a default class / Coldline as the default storage class for the backup data, then click Continue.
- Choose how to control access to objects. Leave the Enforce public access prevention on this bucket option checked, choose the default option Uniform as the Access control type, and click Continue.
- Choose how to protect object data. Leave the options as default for this section.
Note: Since CubeBackup constantly overwrites the SQLite files during each backup, enabling the Object versioning or Retention policy would lead to unnecessary file duplication and extra costs.
- Click Create.
- If prompted with the 'Public access will be prevented' notification, please leave the Enforce public access prevention on this bucket option checked as default and click Confirm.
- Go back to the CubeBackup setup wizard and enter the name of this newly created bucket.
- In the same active project, select IAM & Admin > Service Accounts from the navigation menu.
- Click + Create service account.
- Enter a valid Service account name and a Service account ID will be generated automatically. You can simply use the default one and click Create and continue.
- In the Select a role field, search for the Storage Object User and select it as the assigned role.
- Click Done directly in the Principals with access step.
- On the Service accounts page, click the Email link of the service account you've just created.
- Select the Keys tab of the service account and click Add key > Create new key.
- Select JSON as the Key type and click Create.
- This will download a service account key file to your local machine. Then you can upload it as the Service account key in Step 2 of the CubeBackup wizard.
Encrypt backups: If you want your backups to be stored encrypted, make sure the "Encrypt backups" option is checked.
Tips:
1. Before clicking Next in the CubeBackup setup wizard, we recommend that you download a copy of the encryption key file using the link provided and store it in a separate, safe location. The key is generated locally and is not stored anywhere except on your servers, which means that we at CubeBackup cannot help you if your key file is lost or damaged through server corruption or natural disaster. For more information about rebuilding your CubeBackup instance in the event of a disaster, see: Disaster recovery of a CubeBackup instance .
2. This option cannot be changed after the initial configuration.
3. Data transfer between Microsoft Azure and your storage is always HTTPS/SSL encrypted, whether or not this option is selected.
4. Encryption may slow down the backup process by around 10%, and cost more CPU cycles.
When all information has been entered, click the Next button.
Note: If you plan to back up Microsoft 365 data to Microsoft Azure Blob Storage, we strongly recommend running CubeBackup on a Microsoft Azure Virtual machine (e.g. B2ms instance) to pair with it. Hosting both the backup server and storage on Azure Cloud will avoid the bottleneck of all data moving through a local server and greatly improve backup performance.
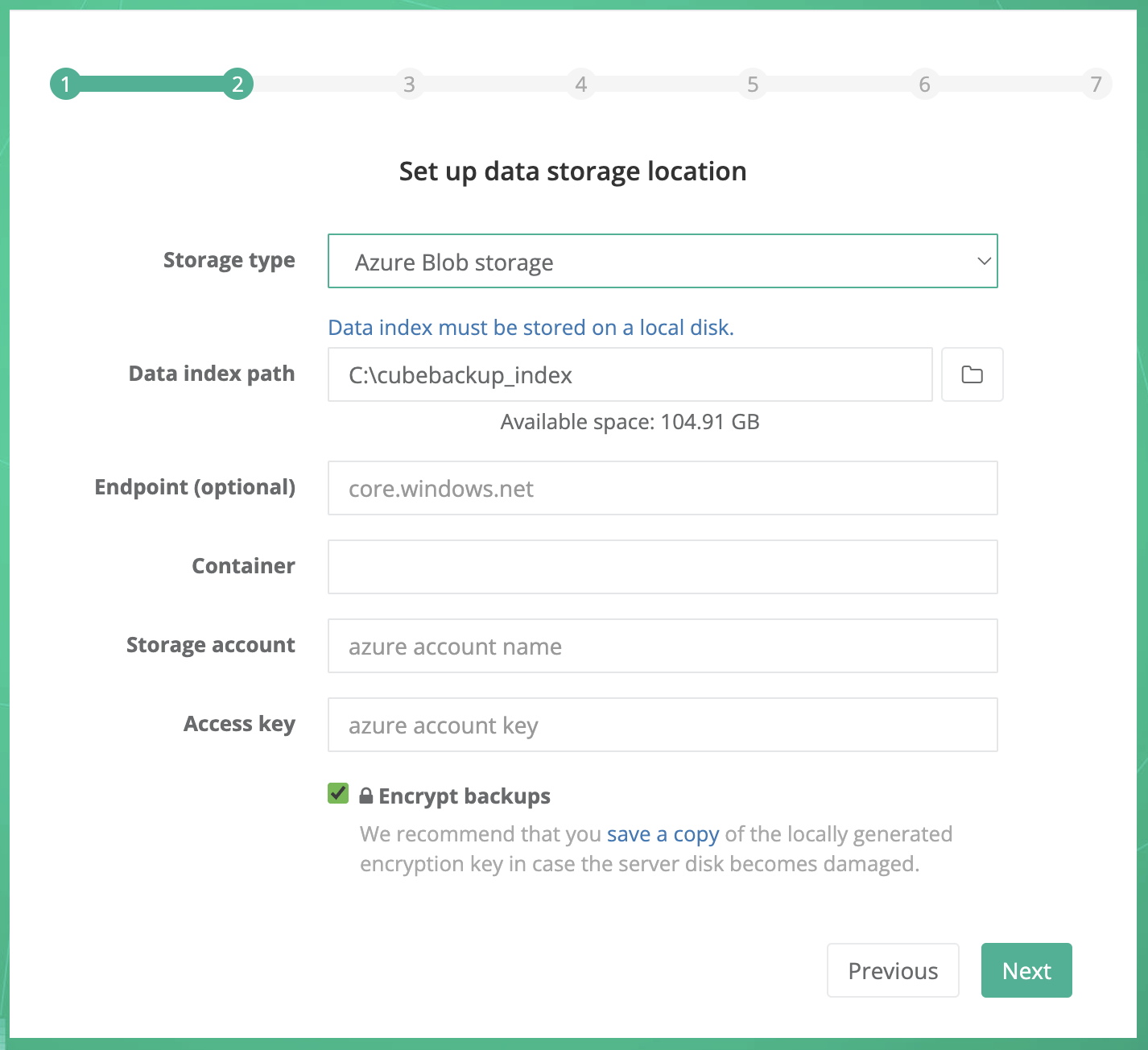
Storage type: Select Azure Blob storage from the dropdown list.
Data index path: Select a local directory to store metadata for your backup.
Note: Since the data index contains the metadata for the backups, access speed is crucially important for the performance of CubeBackup. We strongly recommend that you store the data index on a local SSD. See What is the data index for more information.
Endpoint: (optional) The Blob service endpoint of your storage account.
Container: The container created in your storage account.
Storage account: Your Azure storage account.
Access key: The access key to your storage account.
For more information about Azure Blob storage, storage account, and container, please visit Introduction to Azure Blob storage .
Please follow the instructions below or watch the demo to create a Storage account and a Container for Azure Blob Storage.
Create a storage account
- Log in to the Microsoft Azure Portal using an Azure account with an active subscription. If you do not have an Azure account, sign up to get a new account.
Select Storage Accounts from the left panel and click + Create.
Tip: If you are led back to a welcome page for Azure, it may be because you don't have an active Azure service subscription. In this case, click the Start button below 'Start with an Azure free trial' and follow the instructions to sign up for an Azure subscription.
On the Basics tab, select the Subscription and Resource group in which you'd like to create the storage account.
Next, enter a valid and unique name for your storage account.
Select a Region for your storage account or simply use the default one.
Note: Please select the location based on the security & privacy policy of your organizations. For example, for EU organizations, you may need to select Europe to be in accordance with GDPR.
Select the Performance tier. Standard is recommended.
Choose a Redundancy policy to specify how the data in your Azure Storage account is replicated. Zone-redundant storage (ZRS) is recommended. For more information about replication strategies, see Azure Storage redundancy .
On the Data protection tab, uncheck Enable soft delete for blobs. Since CubeBackup constantly overwrites the SQLite files during each backup, enabling this option would lead to unnecessary file duplication and extra costs.
Additional options are available under Advanced, Networking, Data protection and Tags, but these can be left as default.
Select the Review tab, review your storage account settings, and then click Create. The deployment should only take a few moments to complete.
Go back to the CubeBackup setup wizard and enter the name of this newly created storage account.
Get Access key
To authenticate CubeBackup's requests to your storage account, an Access key is required.- On the Home page, select "Storage Account" > [your newly created storage account]. Then in the detail page, select Access keys under Security + networking in the left panel.
- On the Access keys page, click Show beside the Key textbox for either key1 or key2.
- Copy the displayed access key and paste it into the Access key textbox in the CubeBackup configuration wizard.
Create a new container
- In the detail page of your newly created storage account, click Containers under Data storage from the left panel.
- On the containers page, click + Add container.
- Enter a valid Name and ensure the Public access level is Private (no anonymous access). You can leave the other Advanced settings as default.
- Click Create.
- Go back to the CubeBackup setup wizard and enter the name of this newly created container.
Encrypt backups: If you want your backups to be stored encrypted, make sure the "Encrypt backups" option is checked.
Tips:
1. Before clicking Next in the CubeBackup setup wizard, we recommend that you download a copy of the encryption key file using the link provided and store it in a separate, safe location. The key is generated locally and is not stored anywhere except on your servers, which means that we at CubeBackup cannot help you if your key file is lost or damaged through server corruption or natural disaster. For more information about rebuilding your CubeBackup instance in the event of a disaster, see: Disaster recovery of a CubeBackup instance .
2. This option cannot be changed after the initial configuration.
3. Data transfer between Microsoft Azure and your storage is always HTTPS/SSL encrypted, whether or not this option is selected.
4. Encryption may slow down the backup process by around 10%, and cost more CPU cycles.
When all information has been entered, click the Next button.
CubeBackup supports Amazon S3 compatible storage, such as Wasabi and Backblaze B2 .
- To create a storage bucket on Wasabi Cloud Storage, please refer to Backup Microsoft 365 to Wasabi.
- To create a storage bucket on Backblaze B2 storage, please refer to Backup Microsoft 365 to Backblaze B2.
Note: Usually, S3 compatible cloud storage is not as stable as Amazon S3. Use at your own risk.
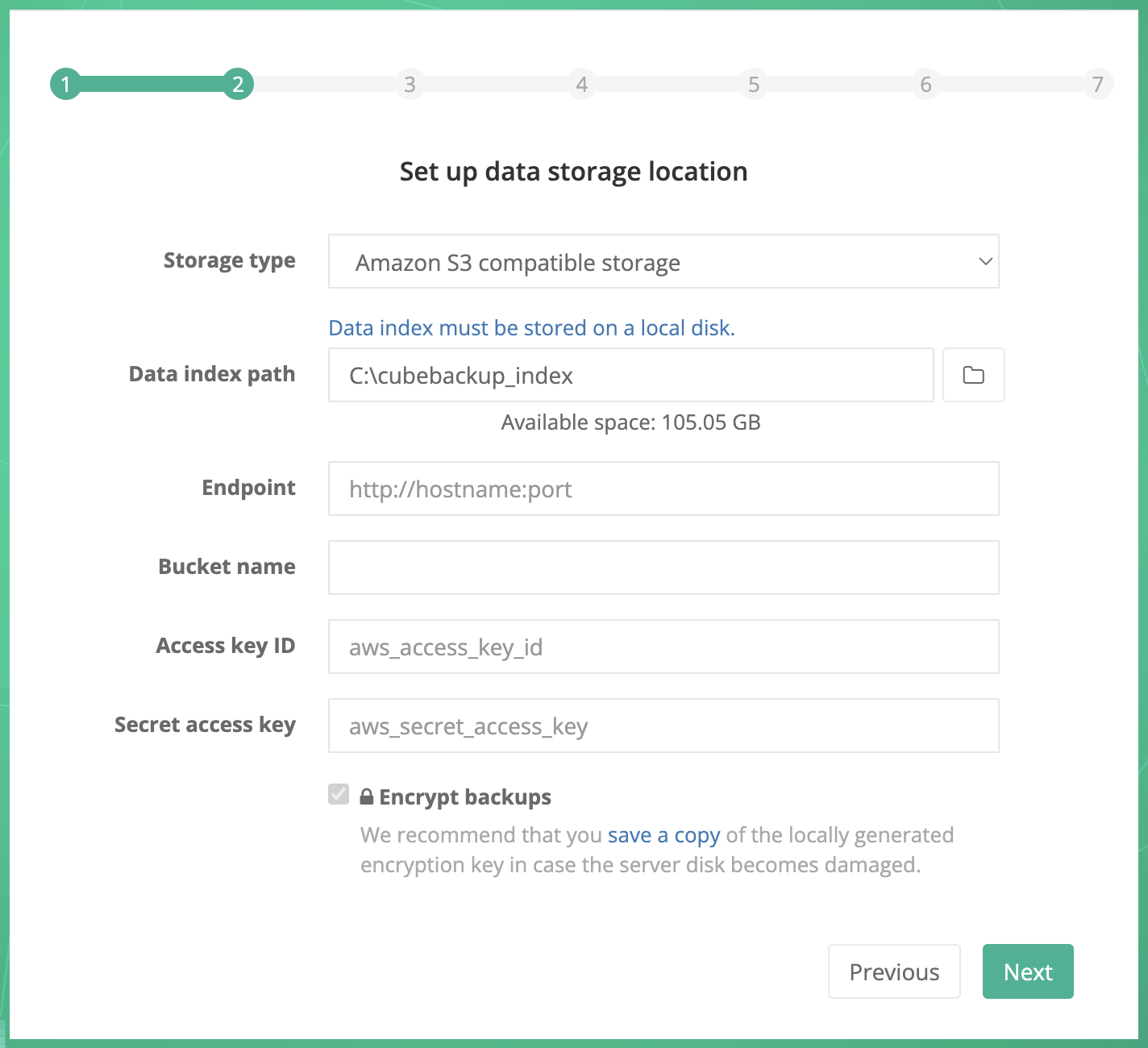
Storage type: Select Amazon S3 compatible storage from the dropdown list.
Data index path: For performance reasons, data index must be stored on a local disk. In most cases, there is no need to specify a new path for the data index.
Note: Data index is the metadata for the backups, and its accessing speed is crucially important for the performance of the backups. We strongly recommend that you store the data index on a local SSD. See What is the data index for more information.
Endpoint: The request URL for your storage bucket.
For Backblaze B2 and IDrive e2 users, please ensure that you prepend https:// to the endpoint address.
Bucket name: Your S3 compatible storage bucket.
Access key ID: The key ID to access your S3 compatible storage.
Secret access key: The access key value to your S3 compatible storage.
Encrypt backups: If you want your backups to be stored encrypted, make sure the "Encrypt backups" option is checked.
Tips:
1. Before clicking Next in the CubeBackup setup wizard, we recommend that you download a copy of the encryption key file using the link provided and store it in a separate, safe location. The key is generated locally and is not stored anywhere except on your servers, which means that we at CubeBackup cannot help you if your key file is lost or damaged through server corruption or natural disaster. For more information about rebuilding your CubeBackup instance in the event of a disaster, see: Disaster recovery of a CubeBackup instance .
2. This option cannot be changed after the initial configuration.
3. Data transfer between Microsoft Azure and your storage is always HTTPS/SSL encrypted, whether or not this option is selected.
4. Encryption may slow down the backup process by around 10%, and cost more CPU cycles.
When all information has been entered, click the Next button.
Step 3. Register and authorize the Microsoft Entra ID (Formerly Azure AD) application for CubeBackup
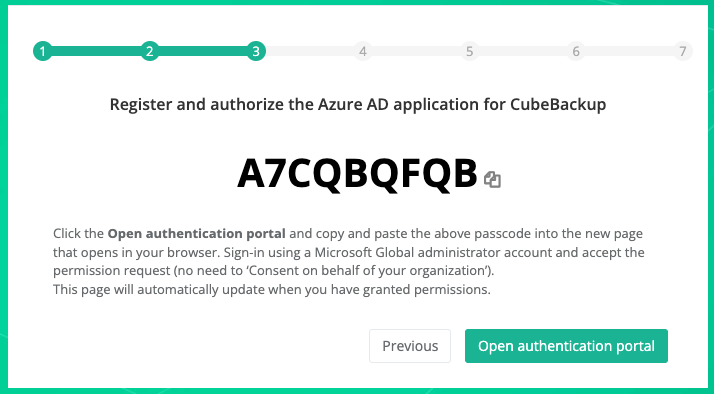
In Step 3, you are required to register and authorize an application in Microsoft Entra ID on behalf of CubeBackup to access resources in your organization.
What is the registered application in Microsoft Entra ID? Why is it needed?
Basically, an application registered in the Microsoft Entra ID (Formerly Azure Active Directory) acts as a service principal, which is used to apply identity and access management (IAM) provided by Microsoft's identity platform, and to authorize unattended operations such as calling APIs. Refer to this doc for more information.
To register your own Microsoft Entra ID (Formerly Azure AD) application in your organization, please follow the steps below:
- Click 'Open authentication portal' in the CubeBackup configuration wizard.
- Copy the passcode and paste it into the authorization page that has opened in your browser.
Please note that the code is valid for 15 minutes. If it expires, you will need to request a new code and try again.
- Sign-in using a Global Administrator account and accept the permission request. You can leave the 'Consent on behalf of your organization' option unchecked.
- Return to the CubeBackup configuration wizard while it performs a few essential steps for creating an Azure AD application, granting permissions, and synchronizing your organizational information. Depending on your organization, this can take as long as ten minutes, so please be patient.
All permissions granted to this new Entra ID application
'CubeBackup'can be viewed here. - If an error message pops up, wait a few minutes and try again. It sometimes takes a while for the application registration and authentication to propagate through Microsoft's servers. If the error persists, feel free to contact us at [email protected].
- The page will update automatically when the process is finished.
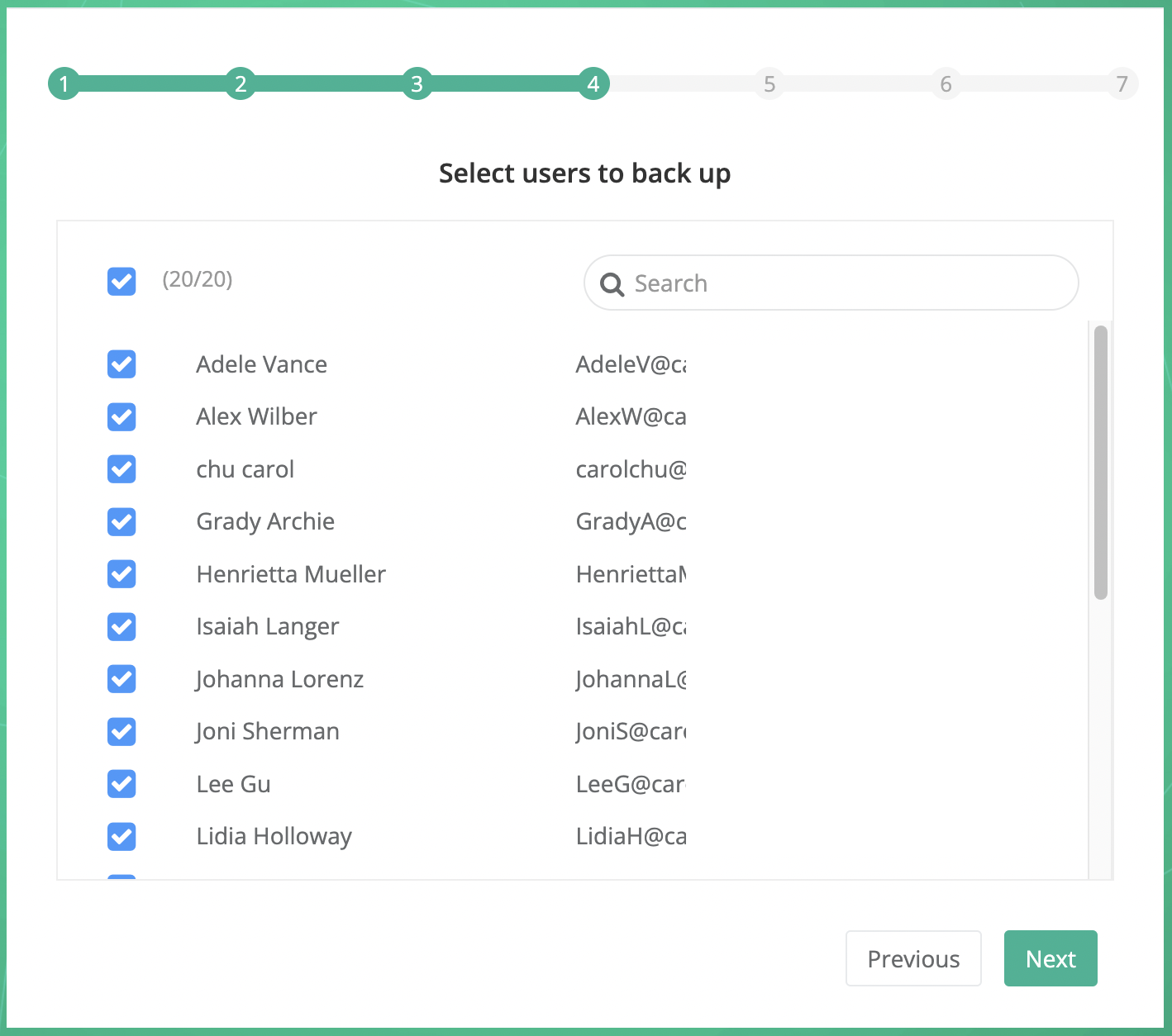
Step 4. Select users to back up
Please select the users in your organization to include in the backup.
All active users are displayed in the list and can be searched by name or email address. In addition to selecting individual users manually, CubeBackup also allows you to select users by teams and groups using the group icon.
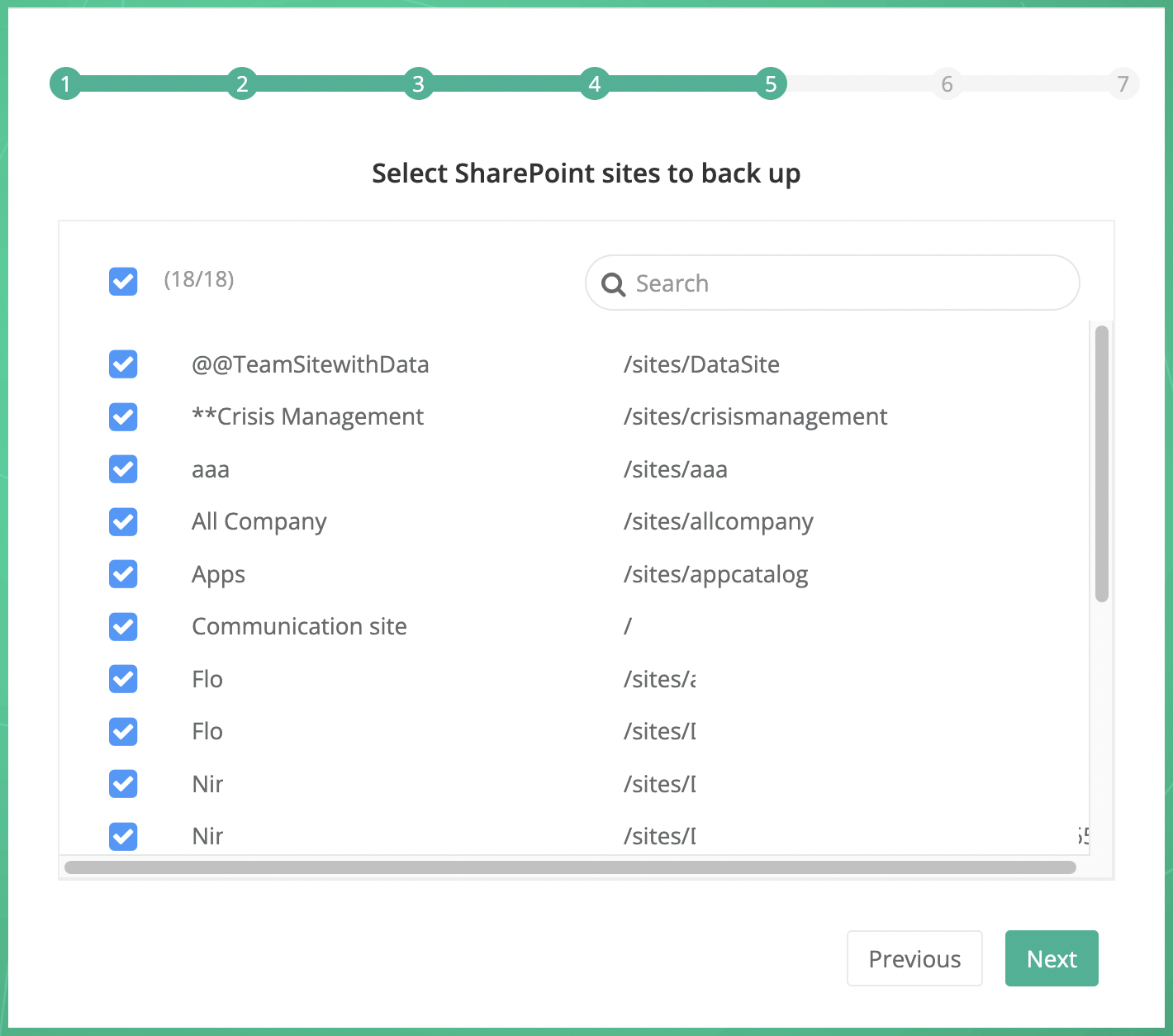
Step 5. Select SharePoint sites to backup
Please select the SharePoint sites in your organization to include in the backup. All active sites are displayed in the list and can be searched by name or URL.
Step 6. Select Teams to backup
Please select the teams in your organization to include in the backup. All active teams are displayed in the list and can be searched by name or description.
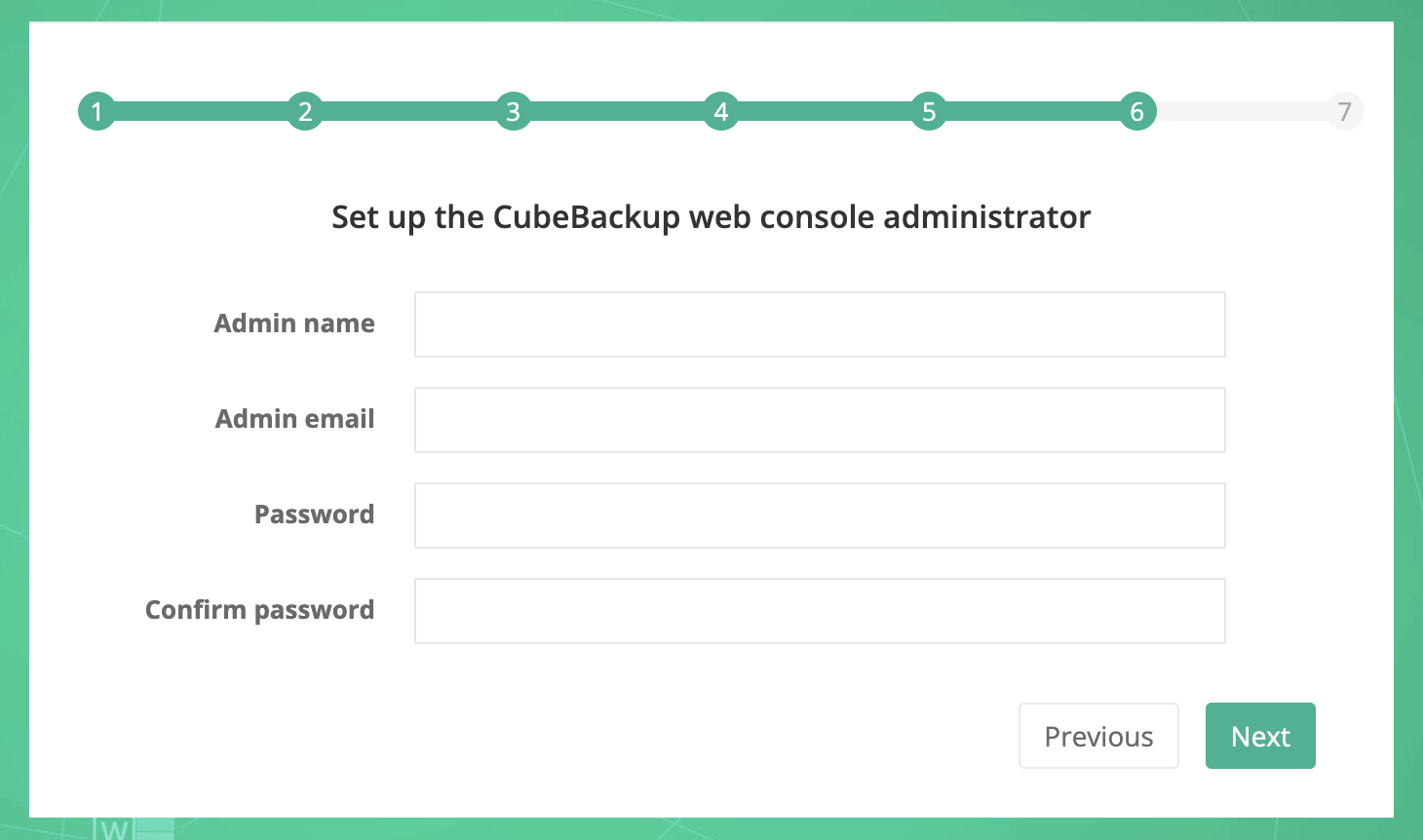
Step 7. Set up the CubeBackup web console administrator
In this step, you will set up the CubeBackup web console administrator account and password.
The administrator account does not need to be the Microsoft 365 administrator of your organization. You can assign any account as the CubeBackup administrator.
This account and password is only for the CubeBackup console; it has no relationship with any Microsoft services.
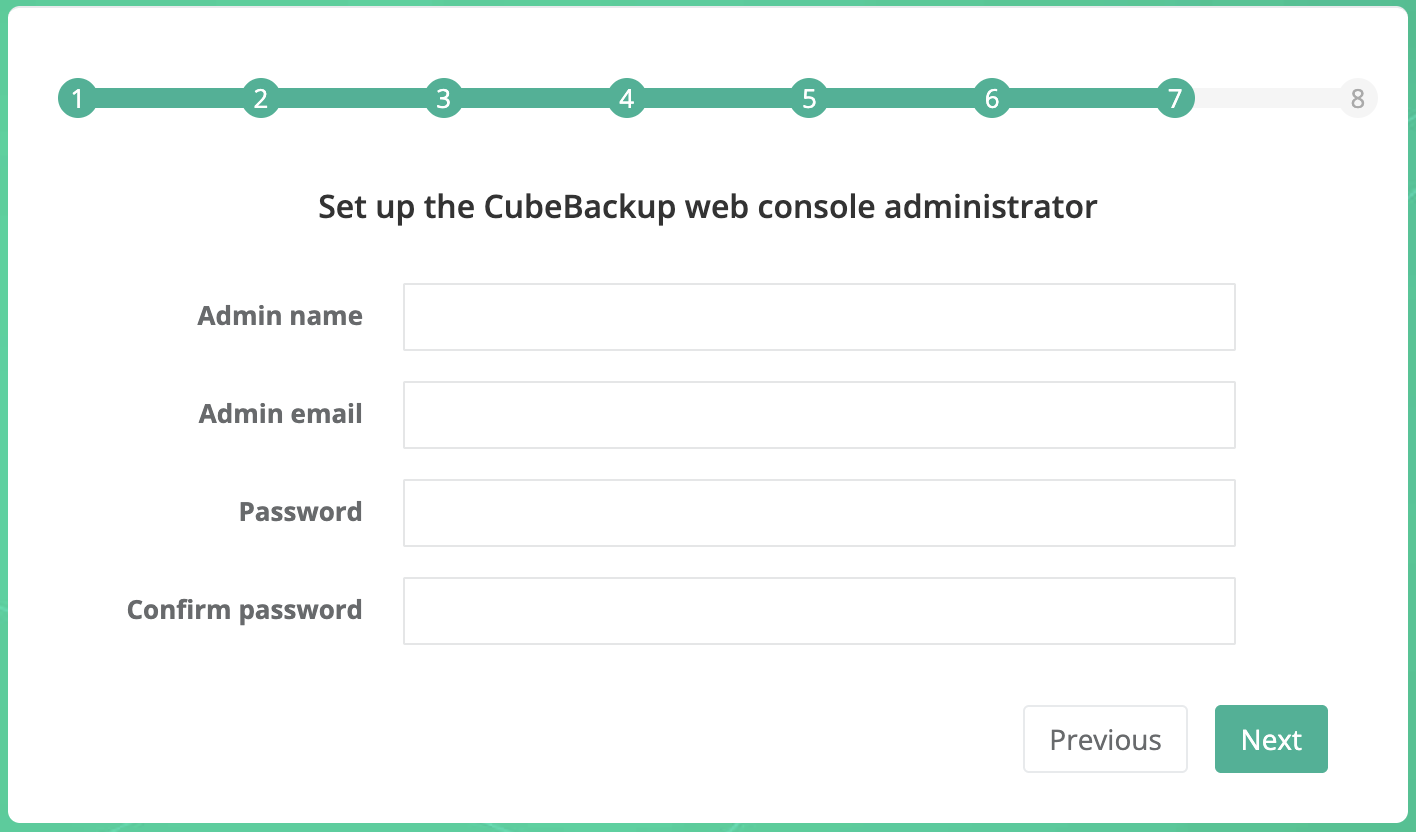
After clicking Next, please wait a few seconds for CubeBackup to be initialized. Then you can log in to the CubeBackup web console to start the backup or configure CubeBackup with more options.
